The Complete Guide to The Risks of Broken Access Control
Learn about what causes broken access controls, the risks and impacts, and how to prevent these vulnerabilities.
Access controls are the process of controlling and monitoring user and application access to resources. This is commonly included under the security domain of Identity and Access Management (IAM). This domain includes four main elements: 1) Identification, 2) Authentication, 3) Authorization 4) Accountability. All four of these elements work together to ensure that all company resources are only accessed by people who should have access to them, for as long as they should have access, and it mandates that user action be monitored to ensure accountability for all users for the actions they perform. One of the biggest vulnerabilities that a company or application can have is the risk of broken access control. One of the most critical vulnerabilities that a company or application can face is the risk of broken access control. In this article, we will break down why this is a huge risk and what can be done to prevent it.
What is broken access control?
Broken access control occurs when an application fails to properly restrict what users can do or access. This allows unauthorized users to perform actions or view data they should not. OWASP broken access control vulnerabilities often stem from missing or inconsistent access control checks. The vulnerability can expose sensitive functions, data, or administrative features. Common examples include forced browsing, privilege misuse, and insecure endpoints that enable unauthorized access. Prevention starts with enforcing consistent authorization logic across every request and user action.
Types of access control
Access control is typically enforced through a combination of role-based rules, object ownership, and contextual validation. The most common types of broken access control risks arise when these rules are applied inconsistently. Weak access control mechanisms allow attackers to bypass access controls by manipulating identifiers, roles, or request context. Proper design ensures that authorization decisions are enforced server-side, not inferred from client behavior.
Vertical access control
Vertical access control restricts access based on user roles or privilege levels, such as standard users versus administrators. Failures here often lead to vertical privilege escalation, where lower-privileged accounts gain access to restricted functions. These flaws occur when access control checks rely on client input or missing role validation. Broken access control mitigation requires enforcing role checks at every sensitive endpoint and validating privileges server-side to prevent access control vulnerabilities from being exploited through crafted requests or direct URL access.
Horizontal access control
Horizontal access control ensures users can only access resources they own or are authorized to view. When implemented incorrectly, attackers can exploit insecure direct object references IDOR by modifying object identifiers to access other users’ data. These issues enable unauthorized access without changing privilege levels. Effective access control remediation includes validating object ownership on every request and ensuring identifiers are never trusted without verification. Strong controls prevent attackers from traversing laterally across accounts or records.
Context-dependent access control
Context-dependent access control evaluates additional conditions such as request origin, workflow state, or business rules. Failures occur when applications ignore context, allowing actions at inappropriate times or states. This can enable unauthorized actions even when roles appear correct. Knowing how to prevent broken access control attacks requires validating context alongside identity and permissions. Broken access control prevention includes enforcing state checks, request sequencing, and conditional logic so authorization decisions reflect real application behavior.
Why is Broken Access Control #1 in OWASP Top 10?
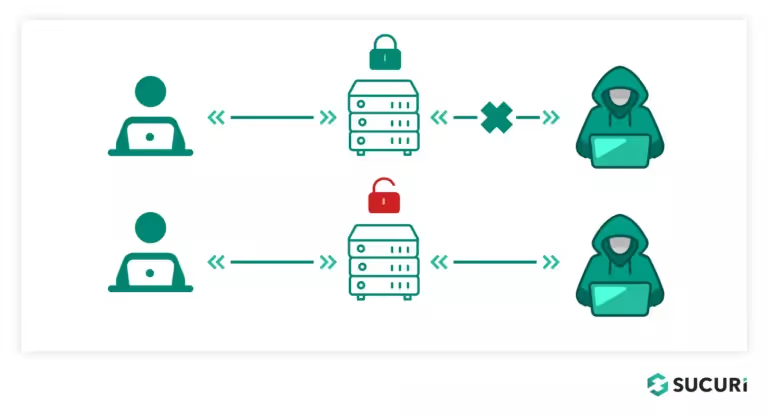
Broken access control can allow attackers an easy pathway to accessing and ultimately attacking company resources. When you think of broken access control, envision having a broken lock on one of the doors of your home. Anyone who tries to go through that door will be allowed to enter. This is a very insecure state, and to a lesser extent, that’s how it is with broken access control. Access control acts similarly to a lock and key, where only users who should have access must be given a key. If you give keys to the wrong people or, worse, the lock isn’t working correctly, people who should not have access will be able to access the resource.
In recent years, broken access control has proven itself to be one of the most prominent vulnerabilities in web applications. In 2021, the OWASP Top 10 list moved broken access control from the fifth position to first on the list of top vulnerabilities in web applications. According to OWASP, 94% of applications were found to have some form of broken access control, with an average incidence rate of 3.81%. Let’s look at some of the reasons why broken access control is on the rise:
Increase in applications: In the last 10-20 years, the amount of digital adoption around web and mobile applications has been huge. Customers now expect most businesses to offer services online rather than solely online. Also, digital expectations were significantly heightened throughout the pandemic, and the application development rush has not subsided since. The more applications there are, the more attack surfaces present themselves.
Increased integration between applications: Applications are becoming more interconnected than ever, and managing exactly what is allowed to talk to can become very complex. This can be due to the number of devices admins must manage, as well as the methods used to connect the devices. Some devices are built to work well together, while others require a more complex solution. Bigger applications also present a larger attack surface with more domains, directories, integrations, functionality, etc.
Insufficient training on secure coding: Many developers simply don’t have a lot of training in creating secure code. As a result, many applications may have access control implementations that are not effective or that are missing altogether. This creates security gaps that allow users to escalate their privileges and gain access that they shouldn't have. If an organization doesn’t have a strong DevSecOps culture, allowing inexperienced developers to set security policies is a recipe for failure.
Multiple IAM Solutions: When trying to integrate a pre-existing identity platform into a new product, the complexity rises as you now need to manage legacy users from the old platform, as well as new users. Using a hybrid of identity management solutions in any scenario can lead to oversights in proper access control.
What might cause a Broken Access Control vulnerability?
- Broken authentication and session management: Broken authentication and session management flaws occur when an application fails to properly validate or protect information associated with user authentication and sessions. An attacker can exploit this to gain access to resources or data they shouldn’t have access to. A common example of this is found with JSON web tokens (JWT). These tokens are commonly used for authentication in web applications. An attack can be performed that changes the signed algorithm of the token, and this can be used to circumvent the authentication method that relies on the integrity of the JWT token.
- Broken Authorization: Authorization refers to the actions that a user is allowed to perform. Typically, any actions that a user is not allowed to perform will not show up in their user interface. However, if access controls are not implemented properly, it’s possible to access functionality intended for a higher privilege level by issuing a direct request to the action/functionality in question. This would be an example of broken authorization in an application. Let's say a web application has an administrative dashboard that only authorized administrators are allowed to access. However, if a regular user can access the dashboard by manipulating the URL, then this is a broken authorization vulnerability. Attackers can use this to access sensitive information, modify or delete data, and perform other cyber attacks.
- Injection flaws: Injection flaws occur when untrusted input is injected into an application, resulting in unintended behaviour. This can be exploited to gain unauthorized access to sensitive data or modify application data. An example of this is cross-site scripting, which is an injection attack that typically uses JavaScript code. Attackers can exploit this to execute malicious scripts in the user’s browser, resulting in session hijacking, cookie theft, or other malicious activity. To detect this type of vulnerability, you should check your application’s source code to ensure that all user input is being filtered/validated before being accepted on the backend.
The impact and risk of Broken Access Controls
- Data Breaches: When a company has broken access controls, it’s easy for an attacker to steal company data. For example, if an attacker can access data in a database through an SQL injection, then they can steal company information, and this would constitute a data breach.
- Potential Privilege Escalation: Privilege escalation is any situation where an attacker can elevate their privileges to achieve a higher level of access. For example, a normal user account through an available exploit can raise their privileges to become an administrator. In this situation, the attacker will be able to perform commands and read data that they shouldn’t be able to.
- Failing Compliance Regulations: If your company has poor access controls and this is revealed through an audit or security testing, then you will be at risk of failing compliance regulations. Many compliance regulations mandate that your company implement strong access control to protect company assets.
- Operation Disruptions: Security incidents due to poor access controls can have a significant impact on company operations. When outside attackers get access to company resources and perform attacks, it can cause outages and service disruptions.
- Reputational/Legal/Financial Repercussions: When hackers get access to company data, it can have several negative impacts on a business. First, there are financial repercussions associated with recovering from the data breach, as well as reputational and legal consequences related to data privacy. Many customers/partners will lose trust in the company if their data is leaked, and some of them may choose to take legal action if they think the company is at fault.
How to Prevent Broken Access Control
Access Validation
Now that we’ve talked about broken access control, let’s look at what proper access control should look like. If an attacker tries to tamper with an application or database by modifying a request to the system, the system should have proper protections in place to recognize an invalid request. Two common examples of this would be SQL injections and cross-site scripting attacks. SQL injections submitted modified SQL statements in an attempt to extract information from the backend database or modify the database itself. To defend against this type of attack, proper input validation should detect invalid requests like this and not allow it to execute.
Secondly, the system should have function-level access control to verify whether the user is authorized to perform their desired action. For example, if someone is on a user account, they should not be able to perform admin actions or raise their privileges to become an admin. In particular, web applications need to rely on server-side access control rather than client-side so that adversaries cannot tamper with it. The application should perform checks at multiple levels, including the data or object, to ensure there are no holes in the process. This includes authorization to make a request as well as authorization to access a particular object in that request.
Thirdly, businesses must constantly review their access control processes and procedures. You should take time to thoroughly review the authorization logic of chosen tools and technology and implement custom logic when necessary. You should also formally test all configurations to make sure there are no workarounds. Additionally, you should do access reviews for employees/contractors within your organization to make sure that no one has additional access above what is needed for their job. All static company resources should be formally authorized and incorporated into access control policies.
Lastly, when it comes to the function of the application, you need to make sure that it is designed correctly. You should forbid access when an authorization check fails; this is part of the principle of “fail-safe”. If an access request or an operation fails, then the application should fail in a state that allows it to remain secure. To ensure this, you should perform unit and integration testing of authorization logic to make sure it is sound and not easily circumvented.
Conclusion
Access control is simply the process of restricting user access to company resources/assets. Broken access control is when there are ineffective or missing access controls that allow users to access resources they shouldn’t have access to. Broken access control is one of the most common and most dangerous types of vulnerabilities for an organization. Organizations must be vigilant in mitigating the risk of broken access control to safeguard their assets and data. Broken access control can affect companies severely by hurting them financially as well as damaging their reputation and business relationships. To prevent broken access control, it’s important to implement and validate that your access controls are working properly continuously.
Broken access control is the most common finding in web application penetration testing and one of the most consistently underestimated in internal reviews, because it requires testing across user roles, session states, and API endpoints in combination. A web application penetration test will map your authorization model and actively attempt to escalate privileges, access other users' data, and bypass role restrictions in ways that automated scanning reliably misses.





.avif)