The Good, The Bad and the Ugly? Lessons from Incident Responses
Learn the Dos and Don’ts for your incident response plan based on real-life incidents. Read here.
Choosing the right penetration testing company can make or break your security strategy. With countless vendors promising quick fixes and flashy reports, finding a team that actually delivers real security insights is tougher than it should be.
In this Software Secured guide, we break down the top 10 penetration testing companies that go beyond the checklist to give you real protection.
Software Secured has spent over a decade in the trenches of cybersecurity, working with SaaS companies that demand more than basic check-the-box testing. Our team delivers manual, high-impact penetration tests that help companies stay compliant and secure. This list reflects what we know from real-world experience, not theory.
We were looking for a penetration testing partner who could give us assurance that our security posture and guide us through what we needed to improve. Software Secured demonstrated their penetration testing expertise, at a competitive price. We were pleased with the results and the communication with Software Secured throughout the process.
Tega McKinney,Director of Engineering at Motiva Ventures
A penetration test is only as good as the team behind it. Pick the right one, and you’ll get real security gains that move your business forward. The right choice ensures:
Next, let's look at 10 penetration testing vendors that actually deliver.
Providers vary widely in methodology, pricing models, response times, and expertise. Before we get to the detailed review, here’s a quick comparison table to help you spot the differences at a glance.
| Vendor | Year Founded | Pentesting Specialities | Industry Served | Best Suited For |
|---|---|---|---|---|
| Software Secured | 2010 | Web, mobile, API, cloud, code review, network | SaaS, Security, FinTech, HealthTech, AI and EdTech | Security-first SaaS startups, scaleups, and compliance-driven teams |
| Cobalt.io | 2013 | Web, mobile, API, network, DAST | Tech, Mid-market, Agile teams | Tech, Mid-market, Agile teams |
| BreachLock | 2019 | Web, mobile, API, network, compliance-focused | SMEs, Enterprises, Regulated sectors | Companies needing scalable, compliance-ready testing |
| HackerOne | 2012 | Web, mobile, API, cloud, bug bounty, AI/LLM | Tech, Enterprises, Government | Teams looking for crowdsourced, continuous vulnerability discovery |
| NetSPI | 2001 | Web, mobile, API, network, cloud, social engineering | Finance, Healthcare, Government | Large enterprises in regulated industries |
| Synack | 2013 | Web, mobile, API, cloud, AI/LLM, attack surface mgmt | Enterprise, Finance, Healthcare | Enterprises needing continuous, AI+human-driven security testing |
| NCC Group | 1999 | Web, mobile, network, cloud, hardware, IoT, blockchain | Finance, Healthcare, Gov, High assurance | Enterprises needing deep technical testing across specialized systems |
| Indusface WAS | 2004 | Web, mobile, API, cloud, compliance support | SMEs, Tech, Retail, BFSI | Teams focused on web app/API security with compliance needs |
| Packetlabs | 2011 | Web, mobile, network, cloud, cyber maturity | Canadian firms, Compliance-heavy sectors | Firms needing rigorous, manual testing with Canadian data residency |
| Evolve Security | 2016 | Web, mobile, network, cloud, social engineering | Mid-market, Education-driven sectors | Companies wanting real-time collaboration and security education combo |
Now, let’s have a deeper breakdown of what each vendor brings to the table.
The first penetration testing vendor on the list is Software Secured.
Since 2010, we’ve been helping SaaS companies get serious about security. Our full-time team of Canadian security experts delivers manual penetration testing that digs deeper than scanners ever could. We don’t just find issues, we give you a clear plan to fix them fast.
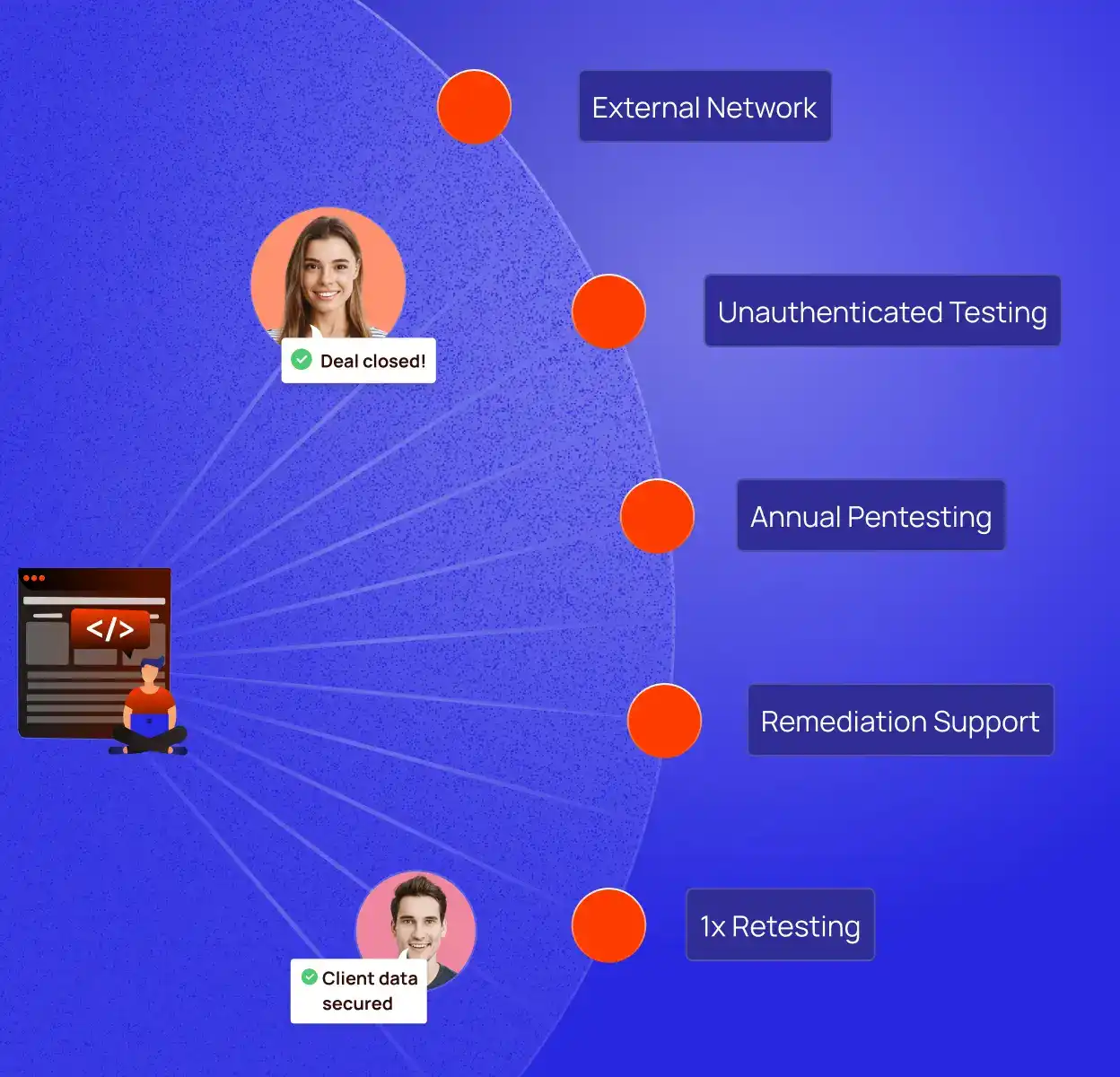
Our pricing is transparent and flexible. Pentest Essentials starts at $5,400, Pentest 360 starts at $10,000. Internal Network Pentest begins at $6,800. We also offer Augmented Security Services and Threat Modeling Solutions for additional security, depending on your needs.
For detailed pricing information, check our pricing page.
We’re built for companies that want real security, not just a checkbox.
Founded in 2013, Cobalt.io delivers penetration testing through their Pentest as a Service (PtaaS) model. They combine a crowdsourced community of security researchers (Cobalt Core) with a SaaS platform that integrates into dev workflows. Their focus is speed, flexibility, and real-time collaboration.
Cobalt.io uses a credit-based pricing model. Credits are bought upfront and used flexibly for different testing needs. Pricing details are custom and vary by scope.
Best for agile teams that need fast, flexible security testing without building a full in-house security function.
BreachLock was founded in 2019 to provide on-demand Pentest as a Service by combining manual testing from certified experts with automated tools. Their client portal provides real-time updates, making it easier for teams to track progress and results.
BreachLock’s offers three different pricing packages: Standard, Extended, Extensive. Each is suited to different organization sizes. Full pricing details only available on request.
Ideal for companies needing scalable, compliance-ready pentesting without building an in-house team.
Established in 2012, HackerOne runs one of the largest bug bounty platforms, connecting companies to a global community of ethical hackers. Their Pentest as a Service taps into this network for rapid, crowdsourced vulnerability discovery.
Pricing depends on scope. Therefore, custom quotes are built around program size and testing needs. You can get one after scheduling a demo.
Great for teams needing fast, flexible security coverage without scaling internal testing teams.
NetSPI was founded in 2001 as a pen testing vendor with a manual-first approach. It’s backed by a large team of in-house certified experts, alongside a PTaaS platform offering real-time reporting and collaboration. NetSPI is a popular choice for big players in highly regulated industries.
NetSPI customizes pricing based on project size and complexity. You’ll need to reach out for a tailored quote.
Best for large organizations in finance, healthcare, and government needing deep, methodical penetration testing.
Blending automation with human expertise, Synack runs continuous penetration testing powered by AI and their vetted Synack Red Team. Since 2013, their platform has given enterprises real-time analytics, asset discovery, and clear vulnerability tracking, designed for companies that need security at scale, not just a once-a-year checkup.
Synack’s pricing is customized based on testing scope and needs. Options range from short-term projects to full continuous testing models.
Great for enterprises needing scalable, always-on security testing with human and AI-driven insights.
Founded in 1999, NCC Group is one of the heavyweights in cybersecurity. With a full-time, global team of certified professionals, they focus on manual, in-depth penetration testing across infrastructure, cloud, and applications for enterprises with complex, high-assurance security needs.
Pricing is fully customized based on scope and project needs. Expect tailored quotes, which are available on request.
Deep technical expertise across domains
Best for enterprises in finance, healthcare, and government needing expert, highly specialized penetration testing.
Operating since 2004, Indusface focuses squarely on securing web and mobile applications. Headquartered in India, they pair traditional penetration testing with their AI-powered AppTrana platform, offering security beyond just vulnerability scans.
Pricing is available on a quote basis. Indusface customizes costs based on the number of apps and complexity of the environment.
Perfect for teams focused on securing web applications and APIs while ticking compliance boxes.
Built in 2011, Packetlabs made its name specializing in deep, manual penetration testing. With an OSCP-certified team and 100% Canadian data residency, they deliver tailored, thorough assessments. Packetlabs’ focus is sharp testing backed by high client satisfaction, not high-volume engagements.
Pricing is custom and based on scope and complexity. You’ll need to request a quote.
Best for Canadian firms or companies wanting rigorous, manual testing with strong compliance and data residency guarantees.
Starting in 2016, Evolve Security set out to combine real-world testing with security education. Their Darwin Attack® portal gives clients real-time visibility into testing progress. Evolve focuses on penetration testing across networks, apps, cloud environments, and even social engineering, with education baked into the process.
Pricing is fully customized. Companies must reach out to get a tailored quote.
Perfect for companies that want real-time collaboration and value security testing paired with education.
Choosing the right penetration testing vendor can make the difference between finding real risks or wasting time. Here’s how to pick the one that fits:
This guide broke down top penetration testing providers and what to look for. Now, let’s talk about one that checks all the boxes - Software Secured.
At Software Secured, we deliver manual, high-impact penetration testing powered by a full-time team of security experts. We help SaaS companies and growing businesses strengthen their security posture, meet compliance requirements, and close real risks, not just check a box.
Our testing is mapped to industry standards, and our approach ensures actionable insights without overwhelming your team. With unlimited retesting and hands-on support, we’re built for companies serious about security.
Ready to get started? Book a free consultation with Software Secured today.
.jpg)
Sherif Koussa is a cybersecurity expert and entrepreneur with a rich software building and breaking background. In 2006, he founded the OWASP Ottawa Chapter, contributed to WebGoat and OWASP Cheat Sheets, and helped launch SANS/GIAC exams. Today, as CEO of Software Secured, he helps hundreds of SaaS companies continuously ship secure code.
Security
Can be easily manipulated without detection if not properly secured.
Digitally signed and can be validated on the server. Manipulation can be detected.
Size
Limited to 4KB.
Can contain much more data, up to 8KB.
Dependency
Often used for session data on the server-side. The server needs to store the session map.
Contains all the necessary information in the token. Doesn’t need to store data on the server.
Storage Location
Browser cookie jar.
Local storage or client-side cookie.
Securing healthcare systems isn’t about buying one flashy tool—it’s about building a hardened stack, layer by layer. Healthcare organizations deal with exposed APIs, legacy systems, undersecured medical devices, and sensitive patient data that hackers actively target. A generic setup won’t cut it.


Providing the quality of the biggest names in security without the price tag and complications.
Manual penetration testing
Full time Canadian hackers
Remediation support
